Security Roles Explained: SOC, GRC, AppSec, and CloudSec: Which Do You Need?
Quick answer: SOC, GRC, and AppSec, CloudSec are four distinct cybersecurity functions. SOC handles threat detection and response. GRC owns governance and compliance. AppSec secures software development. CloudSec protects cloud infrastructure. Treating them as interchangeable roles creates coverage gaps and operational risk.
You’ve seen it happen: A position opens for a “cybersecurity analyst.” The duties include incident response, audit support, vulnerability management, cloud review, and policy documentation. It gets filled. But six months later, alerts are stacking up and audit artifacts are incomplete. IAM issues begin surfacing during a cloud migration.
Did you make a bad hire? Or did you not set up the right structure for the job from the start?
When leaders search for clarity around SOC vs GRC vs AppSec vs CloudSec, what they’re really asking is this: How should a modern security team structure actually work?
The question is complicated because cybersecurity involves several operational disciplines that solve very different problems. If you blend them together, accountability erodes quickly.
Why Hiring “Cybersecurity” as a Category Creates Risk
Budget conversations often push teams toward consolidation. One hire for many responsibilities and maximum efficiency.
In reality, that IT hiring approach usually delays progress.
Compliance deadlines do not slow down because your SOC is triaging an incident. A cloud misconfiguration does not wait until audit season ends. Meanwhile, development teams will continue shipping code.
The friction becomes visible when priorities collide.
The broader labor market compounds this challenge. Research shows that 77% of IT employers report difficulty sourcing skilled talent, and senior-level roles frequently take 90 days or more to fill.
When job listings poorly define roles, replacement takes even longer.
Before you expand headcount, let’s first define ownership. Without that foundation, growth simply multiplies confusion.
SOC: The Operational Front Line
A SOC exists to detect and respond to active threats. In a typical day, security operations center roles handle the following:
- Monitor and triage alerts, including SIEM activity, endpoint telemetry, and anomalies.
- Investigate incidents by determining the scope and root cause, and then containing the incident.
- Escalate events appropriately by coordinating with infrastructure or leadership during material events.
These security operations center roles shorten dwell time and reduce breach impact.
Where organizations struggle is scope creep.
SOC analysts should not be managing policy documentation or drafting audit narratives. When that happens, detection quality suffers.
High alert volume environments feel this first. Fatigue sets in, then turnover rises and knowledge walks out the door.

GRC: Translating Risk Into Business Language
Governance, risk management, and compliance (GRC) operates on a different timeline than SOC. Where SOC responds to what’s happening now, GRC works on a longer horizon: policies, framework mapping, control validation, and vendor assessments.
Strong GRC security responsibilities create defensibility. They ensure that when auditors arrive, documentation exists. When boards ask about risk posture, answers are measurable and clear.
A common misstep is assigning highly technical engineers to GRC roles without evaluating the communication ability. GRC requires clarity about the whole ecosystem, disciplined processes for documenting information, and interacting at the executive level.
It’s technical, but in a different dimension.
If an organization operates under heavy regulation, it should mature its GRC function early. Waiting too long can create compliance problems that take months to fix.
A major insurance company we worked with learned this under pressure.
Application Security: Protecting What You Build
If your team ships code, AppSec belongs in the conversation.
The application security engineer role integrates security into development workflows. That includes code scanning, threat modeling, and embedding controls into CI/CD pipelines.
Without AppSec, vulnerabilities show up after the launch. When that happens, it becomes more costly to fix.
Developers prioritize velocity. Security prioritizes resilience. A capable AppSec function bridges that gap instead of widening it.
Assuming a SOC analyst can transition into AppSec without coding literacy is risky. AppSec demands familiarity with programming languages and development tooling.
The work involves reviewing code and identifying vulnerabilities within applications. This role also collaborates directly with developers to remediate issues before they reach production. Without that foundation, even experienced security professionals may struggle to do an effective job.
Cloud Security: Identity and Infrastructure Governance
Cloud environments amplify configuration risk. A single misconfiguration can expose data, weaken access controls, or create gaps in monitoring. Because cloud infrastructure changes quickly, organizations must continuously validate permissions and network settings to reduce the likelihood of exposure.
The cloud security engineer role focuses heavily on identity, access controls, workload security, and infrastructure-as-code governance.
In cloud ecosystems, identity becomes the control plane. Misconfigured IAM policies can expose data instantly.
As organizations accelerate digital transformation over 12-24 months, CloudSec gaps become visible quickly. Treating CloudSec as an extension of network security misses the architectural differences entirely.
Aligning Security Team Structure With Maturity
There is no universal template for building a cybersecurity team.
Instead, start with exploring your exposure:
- Heavy compliance requirements? Elevate GRC maturity.
- Scaling cloud workloads? Prioritize CloudSec.
- High application velocity? Strengthen AppSec.
- Frequent threat activity? Deepen SOC capacity.
Effective security workforce planning connects business direction with role definition.
When functions blur, accountability diffuses. And when accountability diffuses, issues linger longer than they should.
Evaluate structure before expanding budget. The return on security investment depends more on alignment than on tooling.
Which Should We Hire First?
Start with the question your board or leadership is most likely to ask next quarter.
If it’s likely, “Are we compliant?”, hire GRC. If you’re expecting, “How would we know if we were breached?”, you need SOC.
For “Is our software safe to ship?”, look for AppSec. If it’s “Who’s watching our cloud environment?”, start with a cloud security engineer.
Most organizations eventually need all four disciplines. The sequencing question is where your risk is highest right now and where a gap is most likely to cost you first.
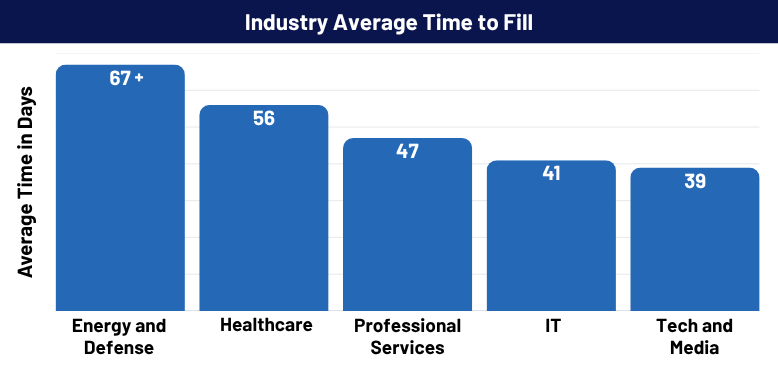
Once you know which role to prioritize, move quickly. As of January 2026, the national average time to fill across all industries runs between 63 and 68 days.
Poorly scoped roles take even longer. When a job description asks one person to cover SOC, GRC, AppSec, and cloud review simultaneously, qualified candidates self-select out.
Defining the role precisely before you post it is the single most effective way to shorten this timeline.

Find the Right Cybersecurity Hire With GDH
If your IT security hiring strategy still revolves around broad “cybersecurity analyst” roles, pause before opening the next requisition.
Reassess ownership and clarify functional boundaries. Your ultimate goal is to align staffing to your current exposure, and that exposure changes over time.
GDH helps organizations match the right cybersecurity talent to the right operational function so hiring investments reduce measurable risk. Contact us to evaluate your current structure.
Frequently Asked Questions
What is the core difference between SOC and GRC?
SOC responds to active threats. GRC manages governance, documentation, and regulatory alignment.
When should you prioritize CloudSec over AppSec?
When cloud infrastructure growth outpaces internal governance and IAM control maturity.
Can smaller organizations combine these roles?
Yes, temporarily. Long term, separating functions improves accountability and scalability.
Why do AppSec and DevOps teams often clash?
Because velocity and control are competing incentives without proper integration.
How do you design an effective security staffing strategy?
Assess regulatory exposure, cloud footprint, development velocity, and incident history before defining roles.








